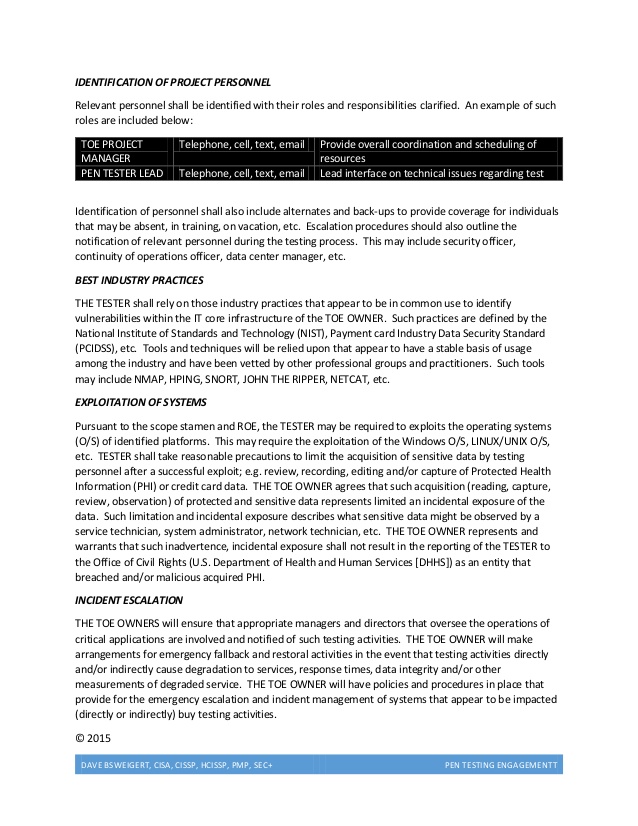
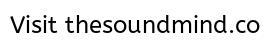
Penetration testing example


Penetration Testing – Complete Guide with Sample Test Cases



Want to find a partner you like Penetration? YES


Penetration Testing Tutorial


Hi, i am Kate Age: 26. Warm towelsLeggy with amazing natural DD- sizes breast and very lovely eyesI'm new out here in Atlanta

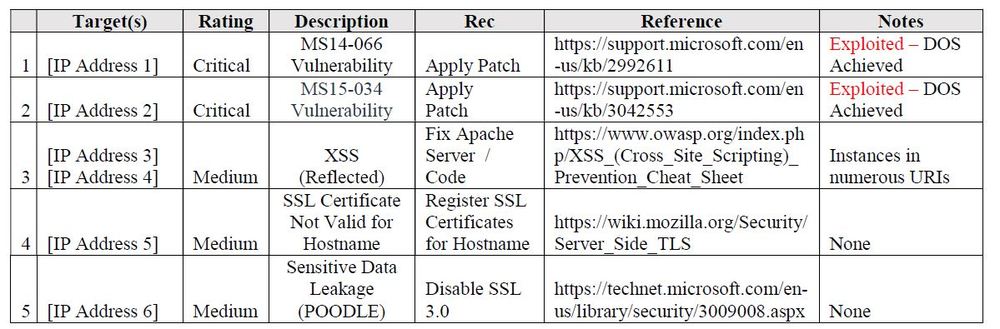
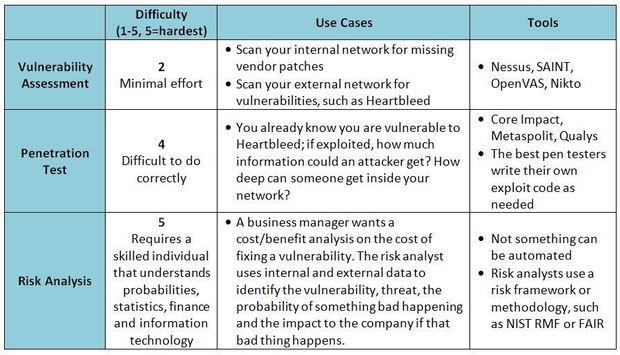
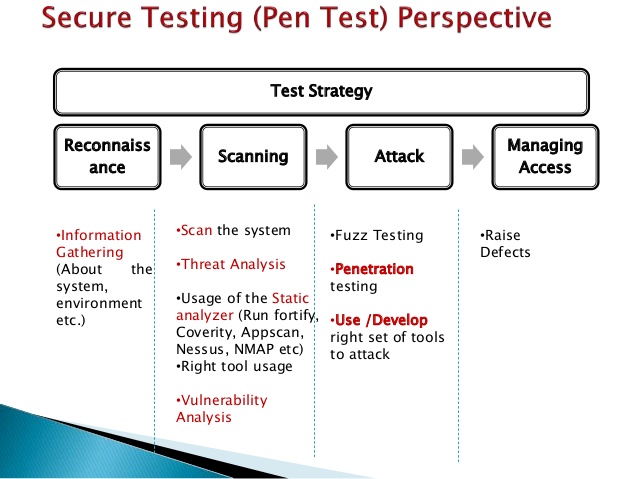
Remember this is not functional testing. In Pentest your goal is to find security holes in the.

Iole Age: 21. Jennifer playful and naughty Melbourne Relaxed and unrushed, Jennifer is available to spend quality time with you for pleasure, fun,travel or dinnerFor more informations text me ;))Oils and lotionsyears old, .
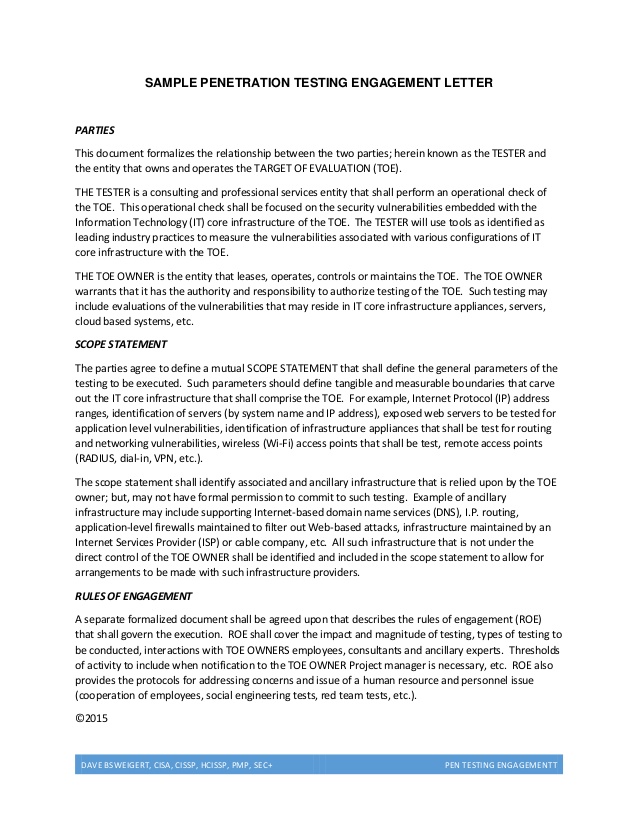
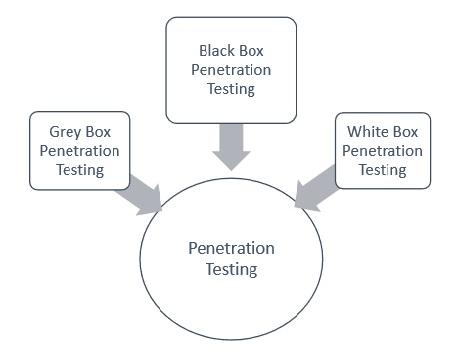
In previous article we seen about “Estimation Guidelines For Testing“. Today we are concentrating on What is Penetration Testing and sample.
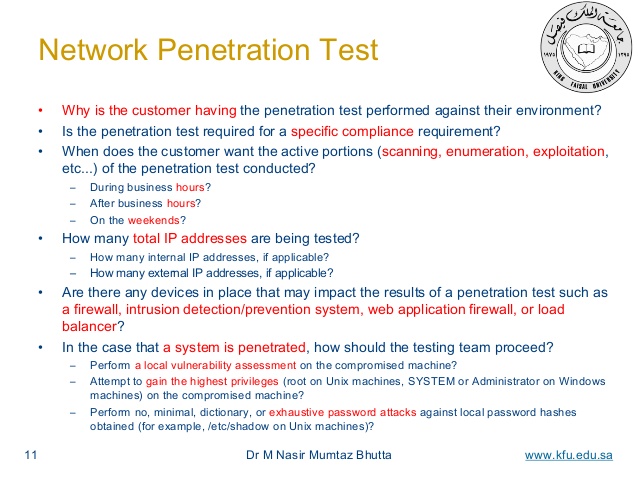
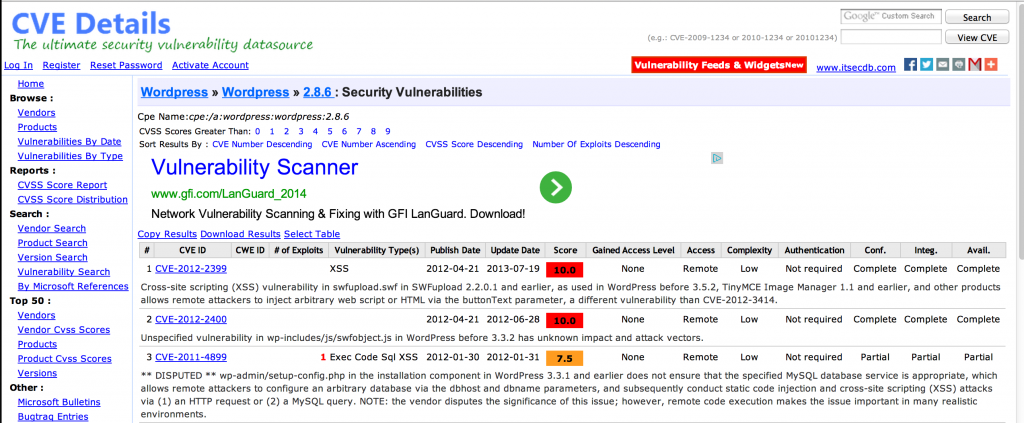
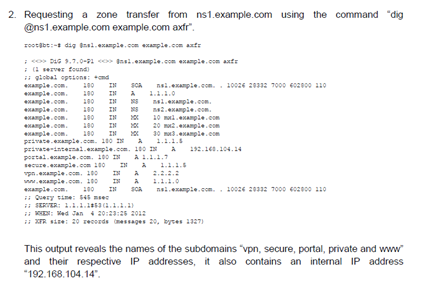
Description:Since you talk of a 'penetration test' you should start with no previous information. For that, you could use nmap. If your objective is no stealth, just use connect scan. If you want to be more stealthy, use syn scan or any of the other scan methods. If you want to use it with other tools, you better configure XML output alongside human, to be able to read it yourself. If you have time, use the full port range and set operating system and service identification -O -sV.































User Comments 1
Post a comment
Comment: